Aes 256 Key Iv Generator
If you are really using a new random key for each message, you can use a fixed initialization vector, yes. But usually you want to reuse a key for several messages - for example, as you somehow have to transfer your key to the receiver of the message, and then using a random initialization vector for each message is important to avoid showing similarities between the messages in the ciphertexts. AES Key Generator Devon 2019-04-27T15:14:21-07:00 Below is a Base64 Encoded AES-256 key which was been generated using the secure javax KeyGenerator. This key will work perfectly with any of the AES encryption code elsewhere on my site, and probably most of yours as well.
- The AES algorithm has a 128-bit block size, regardless of whether you key length is 256, 192 or 128 bits. When a symmetric cipher mode requires an IV, the length of the IV.
- But according to this answer the above key/iv only provide 128 bit security. PHP and Ruby take the key and IV as a binary string. They don't assume that it is Hex-encoded. So, although this key has 256 bits in it, the security is actually only 128 bits, because each character has only 4 bit in a Hex-encoded string.
- RandomKeygen is a free mobile-friendly tool that offers randomly generated keys and passwords you can use to secure any application, service or device. KEY RandomKeygen - The Secure Password & Keygen Generator.
Let's illustrate the AES encryption and AES decryption concepts through working source code in Python.
The first example below will illustrate a simple password-based AES encryption (PBKDF2 + AES-CTR) without message authentication (unauthenticated encryption). The next example will add message authentication (using the AES-GCM mode), then will add password to key derivation (AES-256-GCM + Scrypt).
Simple AES-CTR Example
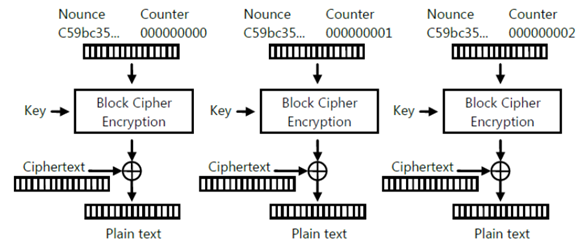
Let's start with simple AES-256-CTR non-authenticated encryption.
Install Python Libraries pyaes and pbkdf2
First, install the Python library pyaes that implements the AES symmetric key encryption algorithm:
Next, install the Python library pbkdf2 that implements the PBKDF2 password-to-key derivation algorithm:
Now, let's play with a simple AES encrypt / decrypt example.
Password to Key Derivation
First start by key derivation: from password to 256-bit encryption key.
Run the above code example: https://repl.it/@nakov/AES-CTR-in-Python.
The above code derives a 256-bit key using the PBKDF2 key derivation algorithm from the password s3cr3t*c0d3. It uses a random password derivation salt (128-bit). This salt should be stored in the output, together with the ciphertext, because without it the decryption key cannot be derived again and the decryption will be impossible.
The output from the above code may look like this:
The derived key consists of 64 hex digits (32 bytes), which represents a 256-bit integer number. It will be different if you run the above code several times, because a random salt is used every time. If you use the same salt, the same key will be derived.
AES Encryption (CTR Block Mode)
Next, generate a random 256-bit initial vector (IV) for the AES CTR block mode and perform the AES-256-CTR encryption:
Run the above code example: https://repl.it/@nakov/AES-encryption-in-Python.
The output from the above code may look like this:
The ciphertext consists of 38 hex digits (19 bytes, 152 bits). Farming simulator product key generator software. This is the size of the input data, the message Text for encryption.
Note that after AES-CTR encryption the initial vector (IV) should be stored along with the ciphertext, because without it, the decryption will be impossible. The IV should be randomly generated for each AES encryption (not hard-coded) for higher security.
Note also that if you encrypt the same plaintext with the same encryption key several times, the output will be different every time, due to the randomness in the IV. This is intended behavior and it increases the security, e.g. resistance to dictionary attacks.
AES Decryption (CTR Block Mode)
Now let's see how to decrypt a ciphertext using the AES-CTR-256 algorithm. The input consists of ciphertext + encryption key + the IV for the CTR counter. The output is the original plaintext. The code is pretty simple:
Run the above code example: https://repl.it/@nakov/AES-decryption-in-Python.
Aes 256 Key Iv Generator Manual
The output of the above should be like this:
Note that the aes object should be initialized again, because the CTR cipher block mode algorithm keeps an internal state that changes over the time.
Note also that the above code cannot detect wrong key, wrong ciphertext or wrong IV. If you use an incorrect key to decrypt the ciphertext, you will get a wrong unreadable text. This is clearly visible by the code below:
Run the above code example: https://repl.it/@nakov/AES-decryption-wrong-key-in-Python.
The output of the above incorrect decryption attempt might be like this:
Now it is your time to play with the above code example. Try to to encrypt and decrypt different messages, to change the input message, the key size, to hard-code the IV, the key and other parameters, switch to CBC mode, and see how the results change. Enjoy learning by playing.
Aes Key Gen
AES-256-GCM Example
Now, let's give a full example how to use the AES-256-GCM symmetric encryption construction. We shall use a different Python library for AES, called pycryptodome, which supports the the AES-256-GCM construction:
Next, let's play with the below AES-GCM example in Python, which generates a random encryption key (secret key) and uses it to encrypt a text message, then decrypts it back to the original plaintext message:
Run the above code example: https://repl.it/@nakov/AES-256-GCM-in-Python.
The AES-GCM encryption takes as input a message + encryption key and produces as output a set of values: { ciphertext + nonce + authTag }.
- The ciphertext is the encrypted message.
- The nonce is the randomly generated initial vector (IV) for the GCM construction.
- The authTag is the message authentication code (MAC) calculated during the encryption.
The encryption key size generated in the above code is 256 bits (32 bytes) and it configures the AES-GCM cipher as AES-256-GCM. If we change the key size to 128 bits or 192 bits, we shall use AES-128-GCM or AES-192-GCM respectively.
The output from the above code looks like this:
It is visible that the encryption key above is 256 bits (64 hex digits), the ciphertext has the same length as the input message (43 bytes), the IV is 128 bits (32 hex digits) and the authentication tag is 128 bits (32 hex digits). If we change something before the decryption (e.g. the ciphertext of the IV), we will get and exception, because the message integrity will be broken:
Run the above code example: https://repl.it/@nakov/AES-256-GCM-wrong-chiphertext-in-Python.
AES-256-GCM + Scrypt Example
Now let's give a more complex example: AES encryption of text by text password. We shall use the authenticated encryption construction AES-256-GCM, combined with Scrypt key derivation:
Run the above code example: https://repl.it/@nakov/AES-256-GCM-with-Scrypt-in-Python.
The above code encrypts using AES-256-GCM given text message by given text password.
During the encryption, the Scrypt KDF function is used (with some fixed parameters) to derive a secret key from the password. The randomly generated KDF salt for the key derivation is stored together with the encrypted message and will be used during the decryption. Then the input message is AES-encrypted using the secret key and the output consists of ciphertext + IV (random nonce) + authTag. The final output holds these 3 values + the KDF salt.
During the decryption, the Scrypt key derivation (with the same parameters) is used to derive the same secret key from the encryption password, together with the KDF salt (which was generated randomly during the encryption). Then the ciphertext is AES-decrypted using the secret key, the IV (nonce) and the authTag. In case of success, the result is the decrypted original plaintext. In case of error, the authentication tag will fail to authenticate the decryption process and an exception will be thrown.
The output from the above code looks like this:
If you run the same code, the output will be different, due to randomness (random KDF salt + random AES nonce).