Jwt Rs256 Generate Key Pair
- Jwt Rs256 Generate Key Pair Number
- Jwt Rs256 Generate Key Pair Number
- Jwt Rs256 Generate Key Pair Free
- Generate Key Code
JSON Web Keys (JWK) can be easilygenerated with the help of the Nimbus JOSE+JWT library:
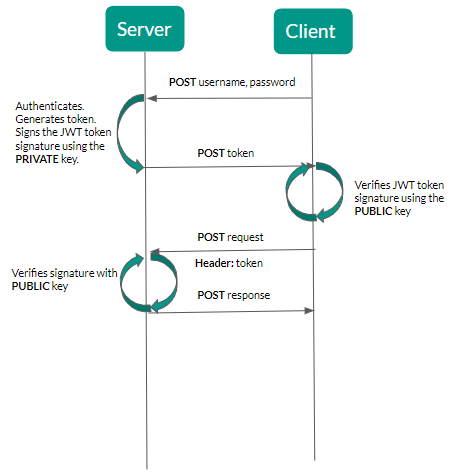
Nov 06, 2019 How to generate JWT RS256 key. GitHub Gist: instantly share code, notes, and snippets. The key to this question is using JWT and Bouncy castle libraries for encoding the token and signing it respectively. JWT for encoding and decoding JWT tokens; Bouncy Castle supports encryption and decryption, especially RS256 get it here; First, you need to transform the private key to the form of RSA parameters. Expose the public key to business client while storing the private key in an encrypted KVM. Use the private key for generating JWT Token. Another public/private key pair will be generated for another api proxy, while verifying the JWT Token and calling end service of the business client. We will expose only the public keys over network during transaction. Please suggest how to achieve it using RSA keys.
Cryptographic keys can also be generated in some other environment and thenconverted into JWK format. Here is an example howto import a key generated with OpenSSL.
You can also check out the command line JWK generator by JustinRicher built with this library.
Jan 06, 2016 In this article we will see how we can verify a JWT token that has been signed with the RS256 algorithm. While there are more than a few libraries for.NET that provide functionality to decode and verify JWT tokens, none of them support the specific algorithm. Jun 10, 2016 You should be able to do so. Generate the key pair into a keystore. The OAuth2 server app uses the keystore to sign the JWT. Export the public key to a file from the keystore to a PEM file(?). RSA is a public-key algorithm. Public-key algorithms generate split keys: one public key and one private key. You deal with a public/private key pair rather than a shared secret.
RSA key pair
The only required parameter to generate an RSA key pair is the key length,which should be at least 2048 bits. There is an alternative constructor in caseyou need to generate weak keys.
The JWK format allows the key to be decorated with metadata. An important pieceof metadata is the key ID ('kid'), for key identification in databases andenabling key rollover. The usage parameter ('use') indicates the key'sintended purpose - signing or encryption.
An RSA key pair can also be generated with the standard Java cryptographicfacilities and then converted to JWK format:
A generated RSA key pair in JWK format:
EC key pair
Elliptic Curve (EC) keys are based on curves with specific mathematicalproperties. The JOSE WG adopted three standardcurves for EC keys and ECoperations with the following designations: P-256, P-384 and P-521.
| EC signature algorithm | Requires EC JWK with curve |
|---|---|
| ES256 | P-256 |
| ES384 | P-384 |
| ES512 | P-521 |
To generate an EC key pair specify its curve:
To generate an EC key pair with the standard Java facilities and convert it toJWK format:
A generated EC P-256 key pair in JWK format:
Octet key pair
Octet key pairs are used to represent Edwards curve keys. They bear the JWKtype designation 'OKP' and are used for JSON Web Signatures (JWS) with Ed25519/ Ed448 and JSON Web Encryption (JWE) with ECDH with X25519 / X448.
Monster hunter generations guide. Starting with v6.0 the Nimbus JOSE+JWT library can generate OKP JWKs with anEd25519 or X25519 curve with help of the optionalTink dependency. Edwards curve cryptographyis not supported by the standard Java JCA yet. For v6.0 of Nimbus JOSE+JWT theMaven dependency for Tink would be
To generate an OKP JWK just specify the name of the Edwards curve and any keymetadata required by your application:
Example Ed25519 key in JWK format:
Octet sequence key
The octet sequence JWK format is intended for representing secret keys, such askeys for use in HMAC and AES. A secret key is essentially a random array ofbytes that cannot be practically guessed.
HMAC key
HMAC computation requires a secret key which length must match the size of theoutput hash. You can also use longer keys, but they will be truncated.
| HMAC algorithm | Required key size |
|---|---|
| HS256 | 256 bits |
| HS384 | 384 bits |
| HS512 | 512 bits |
To a generate a secret 256-bit JWK for HS216:
You can also use Java's SecureRandomor the dedicated KeyGeneratorto generate the key bytes and then use the bytes to create a JWK:
Example secret key in JWK format:
AES key
Symmetric JWE requires an AES key. For example, directencryption with A128GCM requires a 128 bit AES key.
As with HMAC above, you can use the provided the OctetSequenceKeyGeneratoror Java's standardKeyGenerator.
To generate a 128-bit AES JWK directly:
To generate the AES key using Java's standard facility, then convert to JWKformat:
Example 128 bit AES key as JWK:
The jaxrs-jwt quickstart demonstrates a JAX-RS secured application using JSON Web Tokens (JWT) with Elytron.What is it?
This quickstart demonstrates how to secure a JAX-RS service with JWTs using the Elytron subsystem.
There are 4 resource endpoints, plus another one for generating JWTs.
/rest/public- Requires no authentication./rest/customer- Can be accessed by users withcustomerrole authority./rest/admin- Can be accessed by users withadminrole authority./rest/claims- Can be accessed by any authenticated user and demonstrates how to extract token claims./rest/token-POSTendpoint for generating tokens from provided credentials.
| This quickstart asserts only few JWT claims for demonstration purposes. In your application, you should use all claims required by the specification you are using. |
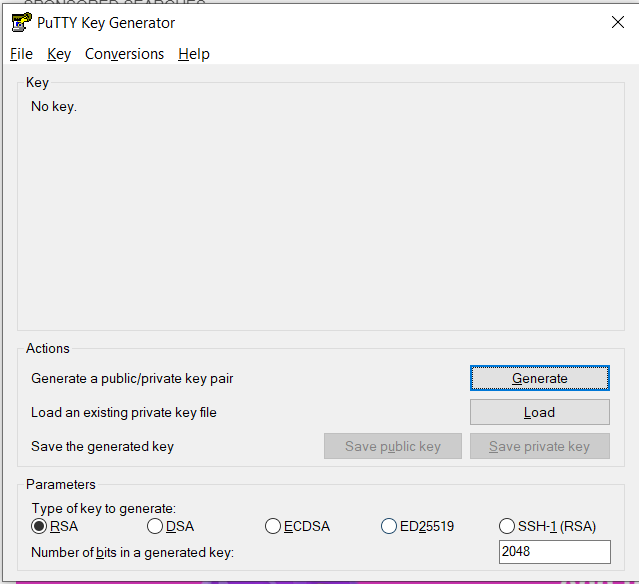
Generate an RS256 Key Pair
Elytron uses RS256 (SHA256withRSA), RS384 (SHA384withRSA), and RS512 (SHA512withRSA) asymmetric keys for signing JWTs. The keys must be in PKCS#8 format.
You can generate your own RS256 key pair using java keytool.
Open a terminal and navigate to the {productName} server
configurationdirectory:Create a keystore for your server using the following command:
Configure the Server
You configure the security domain by running JBoss CLI commands. For your convenience, this quickstart batches the commands into a configure-elytron.cli script provided in the root directory of this quickstart.
Before you begin, make sure you do the following:
Back up the {productName} standalone server configuration as described above.
Start the {productName} server with the standalone default profile as described above.
Review the
configure-elytron.clifile in the root of this quickstart directory. This script adds the configuration that enables Elytron security for the quickstart deployment. Comments in the script describe the purpose of each block of commands.This script contains placeholder PEM public key to make the deployment of this quickstart easy. DO not use this key for anything but testing purposes! You must generate your own key pair for your own application. Open a new terminal, navigate to the root directory of this quickstart, and run the following command, replacing
{jbossHomeName}with the path to your server:For Windows, use the {jbossHomeName}binjboss-cli.batscript.Because this example quickstart demonstrates security, system exceptions are thrown when secured EJB access is attempted by an invalid user. If you want to review the security exceptions in the server log, you can skip this step. If you want to suppress these exceptions in the server log, run the following command, replacing
{jbossHomeName}with the path to your server:For Windows,use the {jbossHomeName}binjboss-cli.batscript.You should see the following result when you run the script:
Stop the {productName} server.
Review the Modified Server Configuration
After stopping the server, open the {jbossHomeName}/standalone/configuration/standalone.xml file and review the changes.
The following
token-realmwas added to thesecurity-realmselement in theelytronsubsystem.The following
security-domainwas added, which uses thejwt-realm.The following HTTP authentication factory was added, which uses
BEARER_TOKENand thejwt-realm.Finally, the application security domain is configured in Undertow to use the new HTTP authentication factory.
Access the Application
Before you run the client, make sure you have already successfully deployed the REST to the server in the previous step and that your terminal is still in the same folder.
Investigate the Console Output
Jwt Rs256 Generate Key Pair Number
When you run the mvn exec:java command, you see the following output.
The client tries to test service functionality using 3 identities.
Jwt Rs256 Generate Key Pair Number
admin- this user belongs to groupadmin, which gives himrights to access/rest/protectedcustomer- this user belongs to groupcustomer, which gives him rights to access/rest/customerno credentials provided - the client tries to access all endpoints, but can only access unprotected
/rest/public
The endpoint /rest/claims demonstrates a way, how you could extract token claims for further manipulation.
Jwt Rs256 Generate Key Pair Free
./shared-doc/undeploy-the-quickstart.adoc:restoreScriptName: restore-configuration.cli./shared-doc/restore-standalone-server-configuration.adoc
Generate Key Code
Generate ssh secret key mac. This script reverts the changes made to the undertow and elytron subsystem.You should see the following result when you run the script.